Why Cybersec Matters More Than Ever
In the modern age of digital data, the concept of a totally secure perimeter is dead.
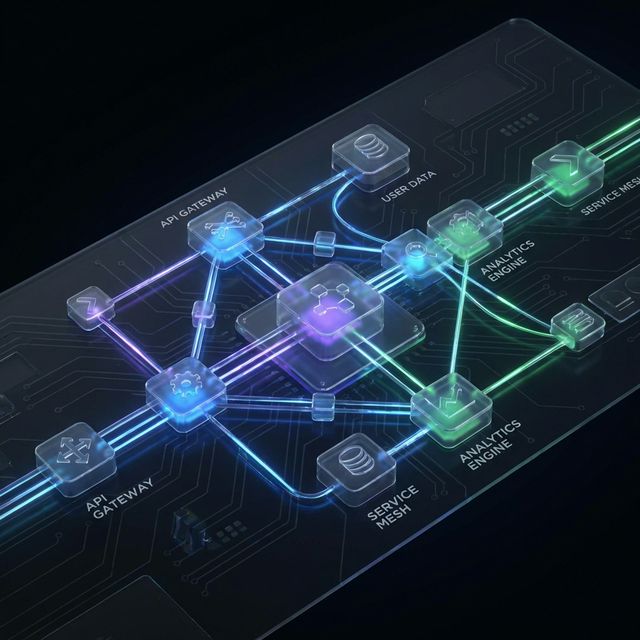
Assume that an attacker is already inside your network. This is the foundation of Zero Trust architecture.
Common Vectors of Attack
When building new applications today, you are responsible for knowing and preventing incredibly common attacks like:
- SQL Injections: Attackers writing SQL in your forms that gets accidentally executed by your database engine.
- Cross-Site Scripting (XSS): Injecting malicious JavaScript payloads into fields that other users then render in their browsers.
- Cross-Site Request Forgery (CSRF): Forcing a user to execute unwanted actions on a web application they’re authenticated in.
Sanitization is the Key
Always sanitize your inputs. Every framework has built-in tools for escaping user input before rendering it or sending it to the database engine. Never trust anything that comes from the client side!